Discussion Overview
The discussion revolves around concerns related to PC security, specifically focusing on firewall parameters, antivirus effectiveness, and network vulnerabilities. Participants share experiences and seek clarification on how to ensure their systems are secure from unauthorized access, particularly in the context of using WLAN and understanding network traffic.
Discussion Character
- Exploratory
- Technical explanation
- Conceptual clarification
- Debate/contested
- Mathematical reasoning
Main Points Raised
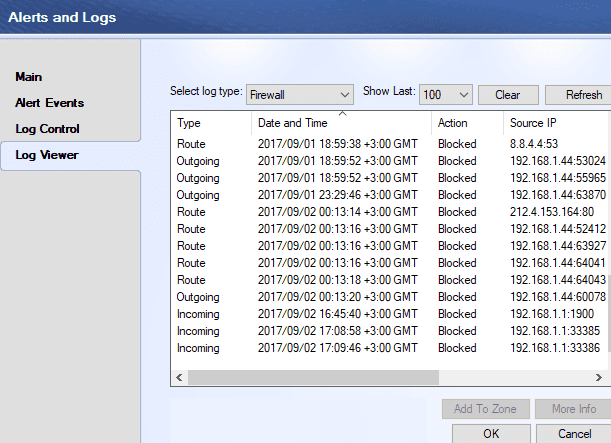
- One participant expresses confusion about unauthorized control of their PC despite having antivirus software and a firewall installed, questioning the effectiveness of these measures.
- Another participant notes that automated tools are constantly scanning for vulnerabilities across devices, including IoT, suggesting that the issue is widespread.
- Questions arise about the meaning of terms like "route," "incoming," and "outgoing" in the context of firewall settings.
- Participants discuss internal IP addresses (e.g., 192.168.x.x) and their implications for network security, suggesting that such addresses typically indicate internal communication.
- There is a discussion about identifying potentially harmful network connections using commands like netstat, with examples provided to illustrate typical local and foreign addresses.
- Clarifications are made regarding port numbers, likening them to phone lines for software communication, and the significance of certain addresses being considered harmless.
- One participant shares a detailed explanation of various IP addresses and their meanings, emphasizing the importance of understanding network configurations.
- Concerns are raised about how to check for unauthorized devices on a WLAN, with suggestions to access router settings for connected devices.
- Participants share experiences and caution against changing router settings without proper knowledge, highlighting the potential risks involved.
- There is a question about whether the term "firewall" refers to software (like Windows Firewall) or a physical device, indicating a need for clarification on types of firewalls.
Areas of Agreement / Disagreement
Participants generally agree on the importance of understanding network security and the potential vulnerabilities present in home networks. However, there are multiple competing views regarding the effectiveness of firewalls and antivirus software, as well as differing interpretations of network traffic and security measures.
Contextual Notes
Limitations include varying levels of understanding among participants regarding network configurations and security measures, as well as the potential for misinterpretation of network traffic data. There are unresolved questions about the effectiveness of different security tools and the implications of various network addresses.
Who May Find This Useful
This discussion may be useful for individuals concerned about their personal computer security, those interested in understanding network configurations, and users seeking to enhance their knowledge of firewalls and antivirus software.
 I'm not a sysadmin but I do end up dealing with it a lot.
I'm not a sysadmin but I do end up dealing with it a lot.